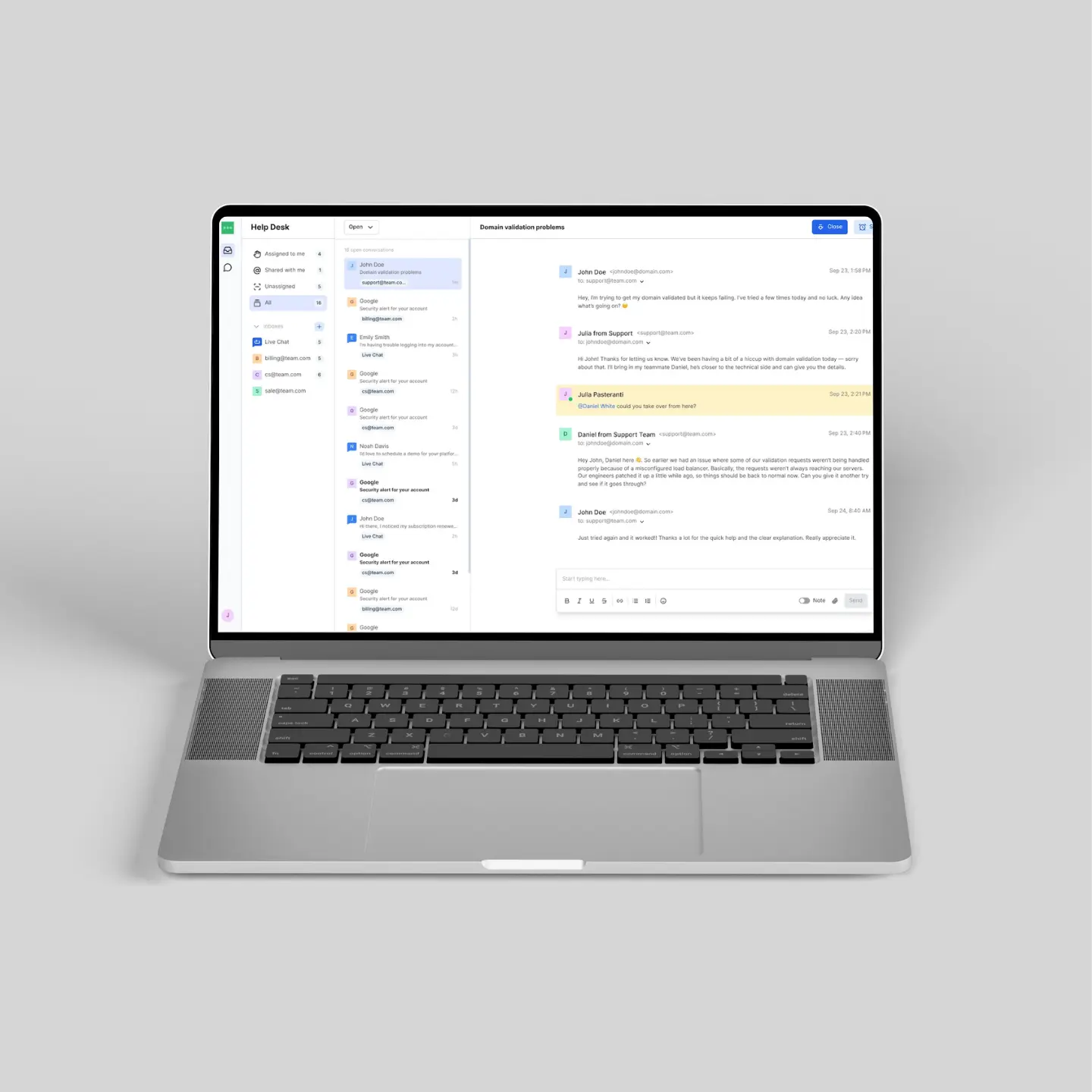
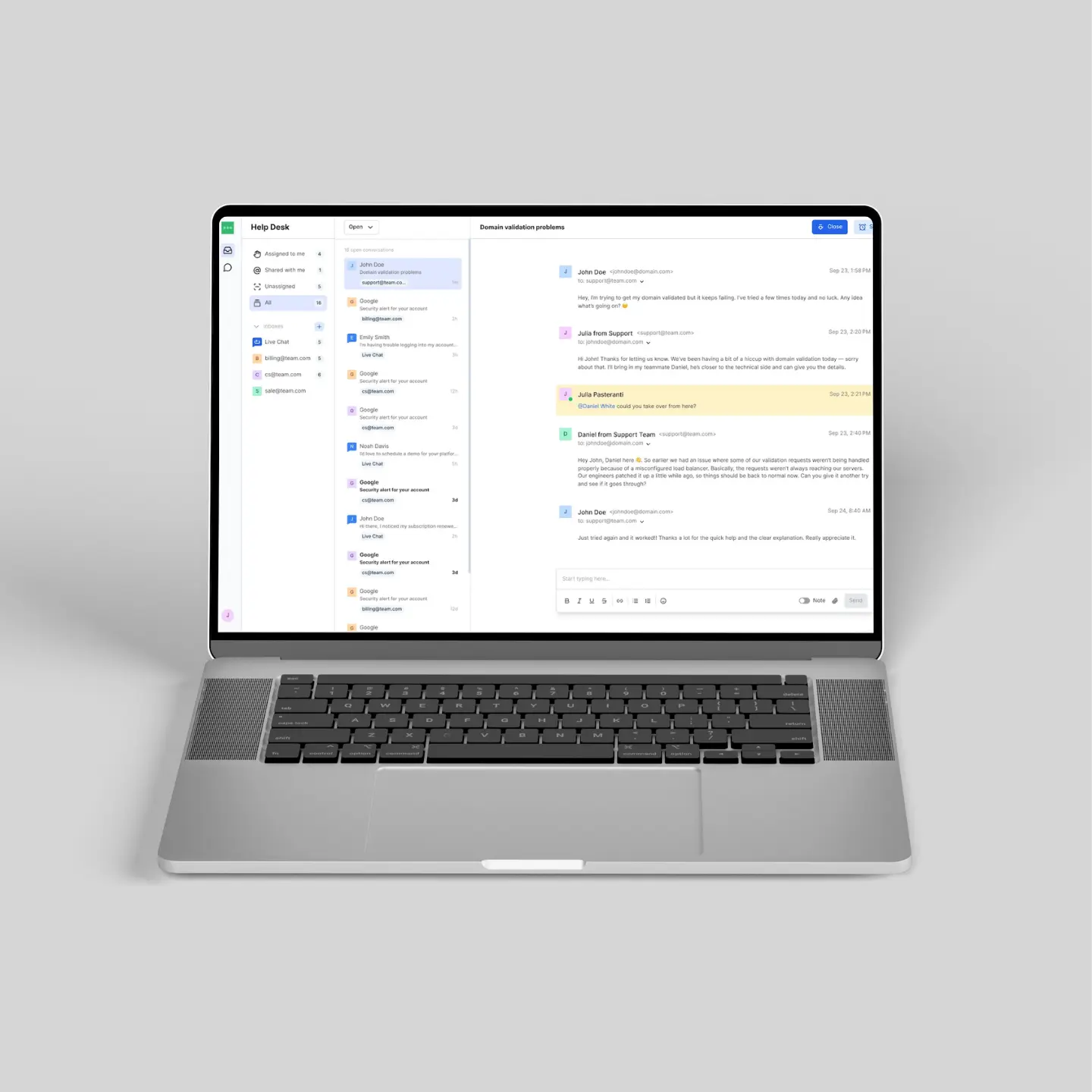
Inbox: Communication Platform
// Core Engineer
Built a real-time communication system as a core contributor. Improved performance and reliability under high load to support low-latency messaging.
// Full Stack Development & AI Integration
// Cybersecurity & Phishing Detection
// Procurement System Development
Conducted comprehensive cross-dataset validation of XGBoost for phishing URL detection across over 760,000 samples. The model achieved 90.7% accuracy, training 12.6x faster and using 3.6x less memory than comparable neural networks.
Built and evaluated a machine-learning browser extension using XGBoost to detect phishing attacks in real-time. The solution accurately identifies malicious URLs while offering an exceptional balance of computational efficiency and interpretability.
// Core Engineer
Built a real-time communication system as a core contributor. Improved performance and reliability under high load to support low-latency messaging.
// Engineer
Contributed to the Elastic Email marketing website. Focused on performance and rendering efficiency to improve user experience.
// Engineer
Worked on a complex, client-heavy email template editor, addressing drag-and-drop integration, state synchronization challenges, and rendering performance for complex layouts.

// have an idea or interesting problem? i’d love to hear about it.